Its quite a tough start for Apple in this New Year 2015. Mac Thunderstrike vulnerability raised a security alarm at apple, and here comes another thunder that targets apple icloud id and password. iDict is a dictionary attack tool that can bypass apple’s two factor authentication system.
There is a new iCloud Apple ID, Password Brute Force Tool available in Internet. As an immediate precaution, you should change your apple id password, if its weak or found in the 500 passwords list that comes with iDict software. Apple ID has recently enabled two factor authentication after massive iCloud password hack happened in 2014. Which led to leak of celebrities nude photos (Rihanna, Kristin Dunst, Kate Upton, Jenifer Lawrance and more) and other sensitive information.

Apple Two Factor authentication is yet to be rolled out for many countries. If you haven’t enabled two factor authentication on your iCloud account, then do it right away. Anyhow, its no more useful as an hacker found another vulnerability in Apple’s iCloud security infrastructure that allows him to bypass restrictions and two factor authentication system in place.
iCloud Password Brute Force Tool
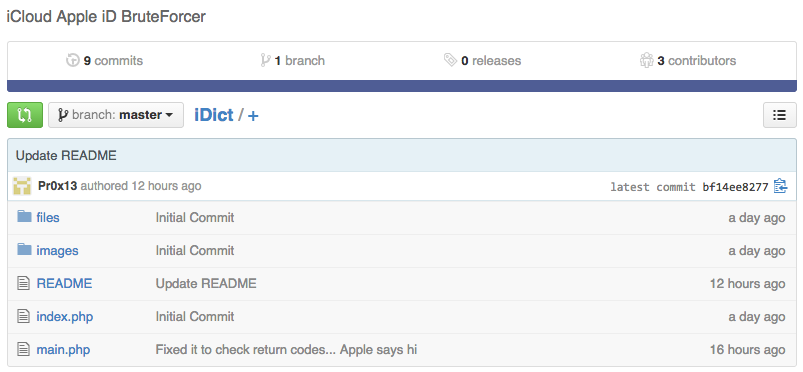
The new iDict iCloud Password Brute Force utility makes the iCloud Two factor authentication useless and bypasses to try random passwords on icloud user accounts. Pr0x13, an hacker hosted the iDict souce code in Github claims that he made this tool publicly available to alert Apple about the serious flaw in their system and they should fix it quickly to prevent huge damage to users privacy and data.
Lets talk about the iDict tool and how it works to penetrate and compromise icloud password. Well, its a regular brute force utility that uses word lists (Password Lists) to attempt on a login system (here, Apple iCloud ID) to find a successful account login that matches the password in the file.
There is no confirmation from security researchers or testers that this tool will work 100% successfully on iCloud accounts. The tool promises it will work 100% on iCloud Apple ID Dictionary attack that bypasses account lockout restrictions and seconday authentication system on any account. If this works as promised, then apple is in serious trouble, with its “Secure” term used in iOS advertisements. It is also recommended for any users to consider using strong passwords to authenticate their Apple iCloud ID. This tool may bypasses the iCloud Two Factor Authentication System in place, but first it works by targeting user accounts that uses passwords that matches with the word lists loaded to the software.
If an hacker come up with massive password list, then this puts lot of iCloud users in risk. But first, it is important to keep a strong, lengthy password to prevent any hack on your iCloud account. Consider trying out Strongpasswordgenerator website to generate a strong password to protect your account from dictionary attacks or brute force attacks.
Some passwords from the list are,
Password1 Princess1 P@ssw0rd Passw0rd Michael1 Blink182 !QAZ2wsx Charlie1 Anthony1 1qaz!QAZ Brandon1 Jordan23 1qaz@WSX Jessica1
You can access the complete 500 words list here at github page.
Whats Next?
Well, we have to wait for a response or a statement saying that the vulnerability in Apple iCloud is fixed and the tool will work no more. As i mentioned earlier, the only option you have right now to protect your iCloud ID is changing the password to something strong and lengthy to prevent being compromised by iDict tool. If you already have a strong password set on your account then you dont have to worry a lot. Apple is known for addressing these type of security issues faster.
Thanks for reading and dont forget to share a word about this article in Twitter, Facebook and Google+. Have a great day.