Bitdefender Total Security Multi-Device 2018 Quick Review
Bitdefender Total Security Multi-Device 2018 brings complete protection to all your Computers (Windows PC, Mac OS X) and (Android) Smartphones. It is incredibly easy to use and brings One Click Security to protect your computer against Viruses, Malwares and Internet Attacks. Bitdefender Multi-Device protection allows…

iDict: New iCloud Apple ID Password Brute Force Tool Released
Its quite a tough start for Apple in this New Year 2015. Mac Thunderstrike vulnerability raised a security alarm at apple, and here comes another thunder that targets apple icloud id and password. iDict is a dictionary attack tool that can bypass apple’s two factor…

What is Thunderstrike? Is my Mac Vulnerable to Hackers?
Thunderstrike is a new security exploit found recently on Mac computers by a Security Researcher Trammel Hudson from Chaos Communications Congress, Germany. Thunderstrike vulnerability allows hackers to infect Thunderbolt Port available older and latest macbook, imac, mac mini computers with a malware. It appears like…
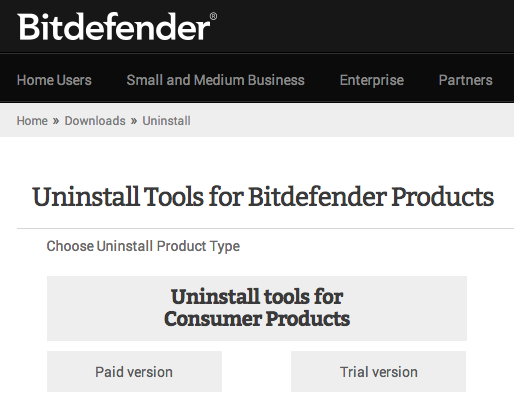
How to Uninstall/Remove Bitdefender Completely?
Installed Bitdefender Antivirus, Internet Security or Total Security recently? Want to uninstall or remove bitdefender completed from your Windows PC or Mac computer? Then this article should help you with the removing or uninstalling bitdefender antivirus completely from your system. Go to bidefender.com/uninstall and download…

mSpy iPhone Spy Software Works Without Jailbreak
Update: mSpy Discount Coupon Code 25% OFF this Christmas. Store wide discount offer for iPhone, Android, Windows PC and Mac OS computers. mSpy the popular iPhone and Android spy software now works without jailbreak. We featured best spy apps for iPhone and android list. You…

Privilege Escalation Vulnerability affects Billions of Android Devices
Newly found Privilege Escalation Vulnerability affects billions of android mobile phones and tablets, except the devices that are running latest Android 5.0 Lollipop. “Privilege Escalation is the act of exploiting a bug, design flaw or configuration in an operating system to gain administrator or root…

POODLE SSL Vulnerability, How to Enable TLS for PHP?
POODLE vulnerability found recently in SSL 3.0 makes the most popularly used Security protocol obsolete and insecure. Google recently announced through webmasters portal, that websites using SSL will have 1% SEO benefit over the sites that are not using it. Recently discovered POODLE vulnerability poses…

5 Best Android Apps for October 2014
We handpicked some of the best and popular android apps for the month of October 2014. Read a short description and begin downloading these super cool android apps that makes your smartphone experience great. The reason we get a smartphone or tablet is to save…